In today's digital age, the threat of Account takeover (ATO) is very real, and businesses and banks are often the primary targets. Imagine being an unsuspecting individual, going about your daily routine, and suddenly, you find yourself targeted by fraudsters posing as bank staff or even state officials. These cunning criminals skillfully manipulate you into revealing sensitive data, and before you know it, they've gained unauthorized access to your online banking, executed stealthy transactions, and siphoned your hard-earned money without raising suspicion. The question is, how can you protect yourself against such a threat?
In an era where technology has made our lives more convenient and connected, it has also opened doors for cybercriminals to exploit vulnerabilities in our digital lives. Account takeover attacks have become increasingly sophisticated, making it essential for individuals to educate themselves on the risks and take proactive measures to safeguard their financial well-being.
Understanding the Anatomy of ATO
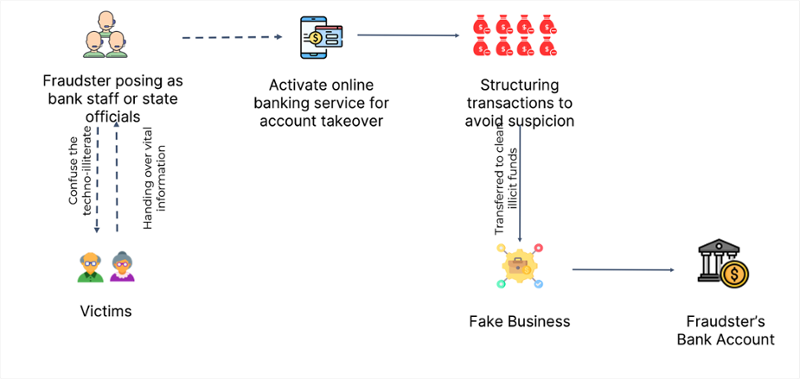
Account Take Over typically unfolds in a series of well-coordinated steps, each designed to maximize the fraudsters' chances of success:
1. Impersonation
Fraudsters often begin by posing as legitimate figures, exploiting your trust in authorities, whether they pretend to be bank representatives, government officials, or even law enforcement officers. These individuals are skilled at impersonating trustworthy figures, using tactics such as creating fake websites or sending convincing emails that appear to be from reputable sources. They prey on your faith in these institutions, hoping to trick you into sharing sensitive information without raising suspicion.
2. Social Engineering
Social engineering is a deceptive technique employed by fraudsters to extract login details and personal information from unsuspecting individuals. It involves psychological manipulation and exploiting human vulnerabilities rather than relying solely on technical hacking methods. These cybercriminals are adept at using social engineering tactics to gain unauthorized access to sensitive data.
3. Online Banking Activation
With stolen data in hand, the fraudsters move on to the next phase of their account takeover operation – activating online banking services using the victim's credentials. This step is crucial for them to gain full access to the victim's account and execute their fraudulent activities undetected.
4. Transaction Structuring
To avoid detection and fly under the radar, cunning fraudsters employ a clever tactic of dividing their illicit gains into smaller, less conspicuous amounts. By doing so, they effectively manage to maintain a low profile and stay clear of any suspicion. This strategic approach enables them to evade detection by financial institutions and law enforcement agencies, ensuring that their fraudulent activities remain undetected for as long as possible.
Identifying Red Flags
Awareness is your best defence against ATO. Here are some important red flags to watch out for:
- Multiple Failed Login Attempts: An unusually high number of failed login attempts can be indicative of a brute force attack. This occurs when an attacker systematically tries different combinations of usernames and passwords until they find the correct one, gaining unauthorized access to an account. Brute force attacks are a common method used by cybercriminals to breach accounts and steal sensitive information.
- Account Detail Modifications: Unexplained changes to your email address, phone number, or personal information should raise immediate suspicions. It is crucial to stay vigilant and monitor any modifications made to your account details. Cybercriminals often target individuals by attempting to change their contact information, such as email addresses and phone numbers, to gain unauthorized access to their accounts. These changes are usually made without the account holder's knowledge or consent and serve as a way for fraudsters to take control of the account and carry out their illicit activities undetected.
- Suspicious Transactions: Keep an eye out for unusual financial activities that don't align with your regular behaviour. This could include unexpected withdrawals, payments to unfamiliar recipients, or sudden and significant increases in spending. Remember, staying vigilant and proactive is key to protecting yourself against the threat of account takeover and financial fraud.
- Swift Fund Movements: Rapid transfers and redirected funds can be a sign that something is amiss. In today's fast-paced, interconnected world, where financial transactions can happen with just a few clicks, it is crucial to stay vigilant and monitor any swift fund movements that deviate from your normal banking behaviour. These sudden and high-speed transfers can indicate potential fraudulent activity or unauthorized access to your accounts.
Leveraging Collective Intelligence for Protection
In the face of evolving digital threats like ATO, it's crucial to stay informed and proactive. The global experts at the AFC Ecosystem (Anti-Financial Crime Ecosystem) recommend monitoring the following scenarios:
- Structuring of Significant Transactions: Be wary of significant transactions being split into multiple smaller ones to avoid disclosure thresholds. By splitting large transactions into multiple smaller ones, fraudsters aim to fly under the radar and make their illicit activities less conspicuous.
- High-Value Transactions: Pay attention to a sudden increase in the value and/or volume of transactions by a particular entity within a short period. This can be a clear indication of potential fraudulent activity or money laundering.
- Newly Registered Entities: Entities that are newly registered but engaged in high-value transactions can be a cause for concern. The emergence of newly registered entities engaging in high-value transactions should raise a red flag and prompt further investigation. While it is not uncommon for legitimate businesses to start afresh and engage in significant financial activities, it is important to exercise caution and verify the legitimacy of these entities.
If you are a financial institution, get in touch with our team today to discover how you can harness the strength of our community and shield your business from the ever-growing threat of ATO. Here at the AFCEcosystem, we believe that collective intelligence is the ultimate defence against regulatory risks and the ultimate way to keep your valuable assets safe.
Through the power of collective intelligence, we analyze and share valuable insights on emerging trends, attack techniques, and best practices. By leveraging the expertise of our community, you can proactively identify and mitigate potential risks before they impact your business. Our collaborative approach allows us to pool resources, share information, and collectively strengthen our defenses against ATO and other financial crimes.
Anti-Financial Crime Compliance with Tookitaki?



